General practices
- Access to all internal systems is protected by multi-factor authentication.
- Access is restricted to those who require it to perform their job, and is regularly reviewed and revoked upon termination or when no longer needed.
- The entire codebase is open-sourced on GitHub. Code reviews are mandatory for all code changes.
- The software components are monitored for CVEs.
- 3rd party conducts penetration tests annually.
- We don't copy production data to external devices such as personal laptops.
Bytebase overall architecture
- Backend is written in Go.
- Frontend is written in TypeScript and Vue3.
- Metadata is stored in PostgreSQL.
- The Bytebase release is a single Go binary that uses Go embedding to embed the frontend assets as well as the PostgreSQL binary. In another word, one can start Bytebase simply by ./bytebase.
- One can store the metadata in an external PostgreSQL instance instead of the embedded one.
Bytebase Cloud
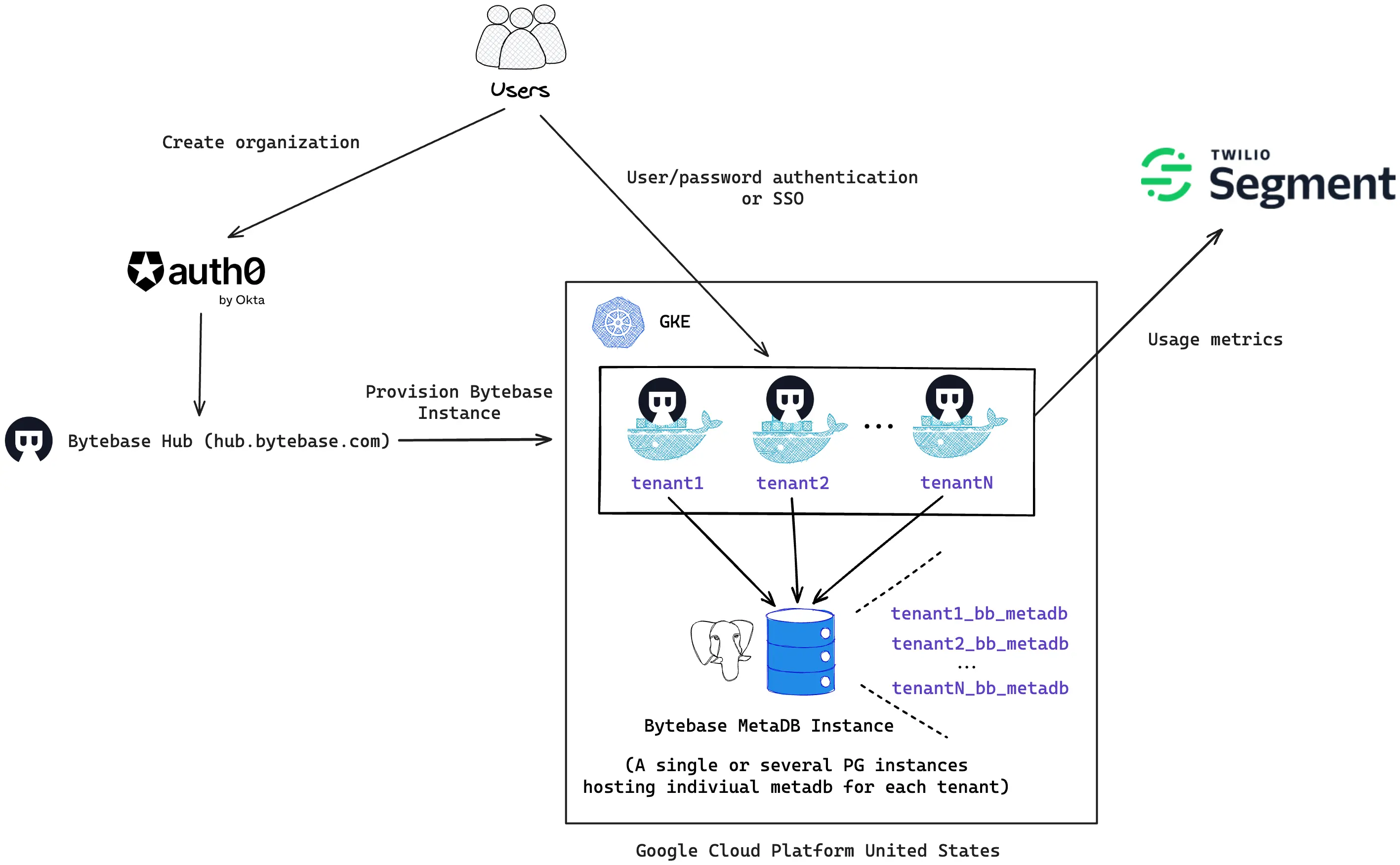
- All infrastructure is hosted on Google Cloud Platform us-central region and managed through Terraform.
- Each customer Bytebase workspace is running inside a separate container managed by Google Container Engine (GKE).
- The metadata is stored in a shared pool of Google Cloud SQL PostgreSQL instances. Storing metadata in a dedicated PostgreSQL instance is available in our Enterprise plan upon request.
- User authentication with the Bytebase Hub is via Auth0.
- Anonymous usage metrics are collected and sent to Segment. Collection can be disabled upon request in our Enterprise plan.
- The customer Bytebase workspace will be deactivated automatically if there is no traffic in 48 hours. The data will be purged in 60 days after deactivation.
Bytebase self-hosted
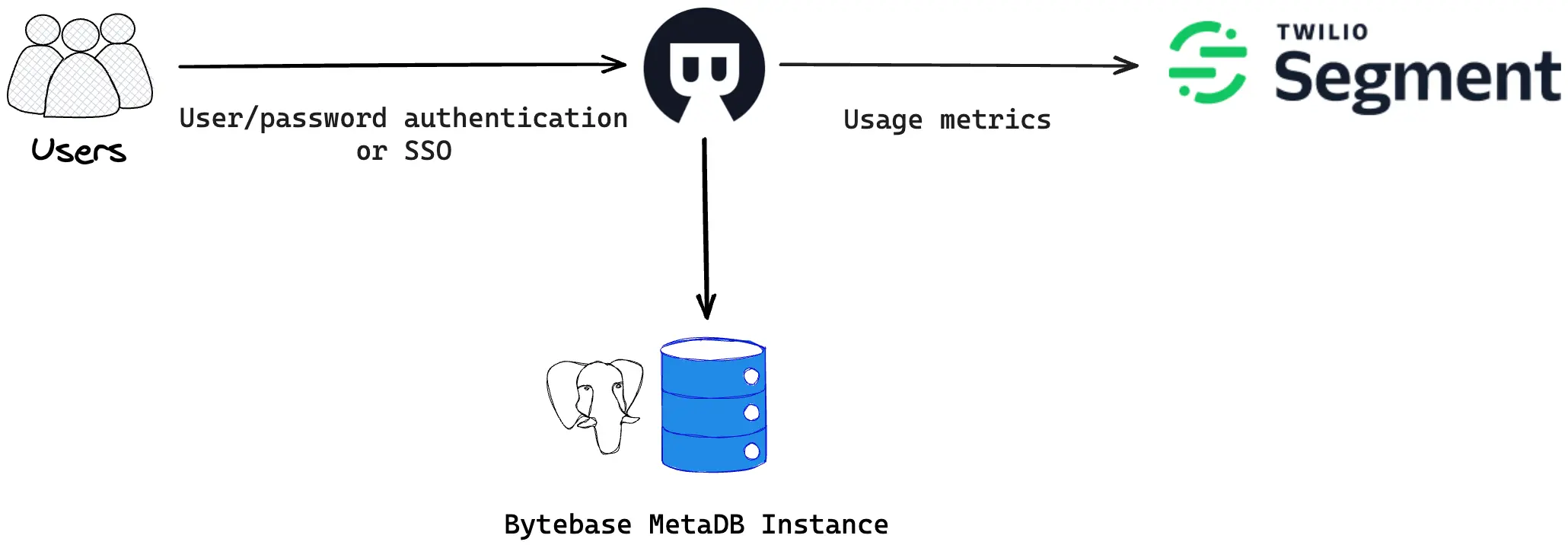
- The architecture is similar to Bytebase Cloud. You can run Bytebase inside docker or on bare-metal.
- Anonymous usage metrics are collected and sent to Segment. Collection can be disabled in the workspace settings.
Shared practices between Bytebase Cloud and self-hosted
- The registered email and name of the first member is sent to Bytebase. We use this to contact regarding sales opportunity, security updates, policy updates, and product updates.
- User/password authentication is enabled by default. SSO with the Bytebase workspace is configurable via OAuth, OIDC, or LDAP. 2FA and Sign-in restriction can be further enforced in the Enterprise plan.
FAQ
Which certification does Bytebase have?
SOC 2 Type II.
Which data does Bytebase store?
Bytebase stores the following data:
- Database connection info.
- Database schema.
How do I report a potential vulnerability or security concern?
Please contact us by e-mail at support@bytebase.com and we'll get back to you ASAP.
